
Sophos Firewall v21.5 introduces native NDR, Entra ID VPN SSO, integrated DNS Protection and enhanced scalability—secure and optimize your network today.

Curious about the security of your smart devices? Learn how PumaBot, a new botnet targeting IoT gadgets, jeopardizes privacy and safety in modern homes.

As cyber threats multiply, businesses must stay vigilant. Discover the rising tide of sophisticated malware and how to protect your organization in this evolving landscape.

As self-improving AI transitions from fiction to reality, we must explore its potential, ethical implications, and safety concerns in this groundbreaking technology.

Unlock the secrets of workplace efficiency as AI revolutionizes productivity. Discover how these technologies streamline operations and enhance performance for businesses.
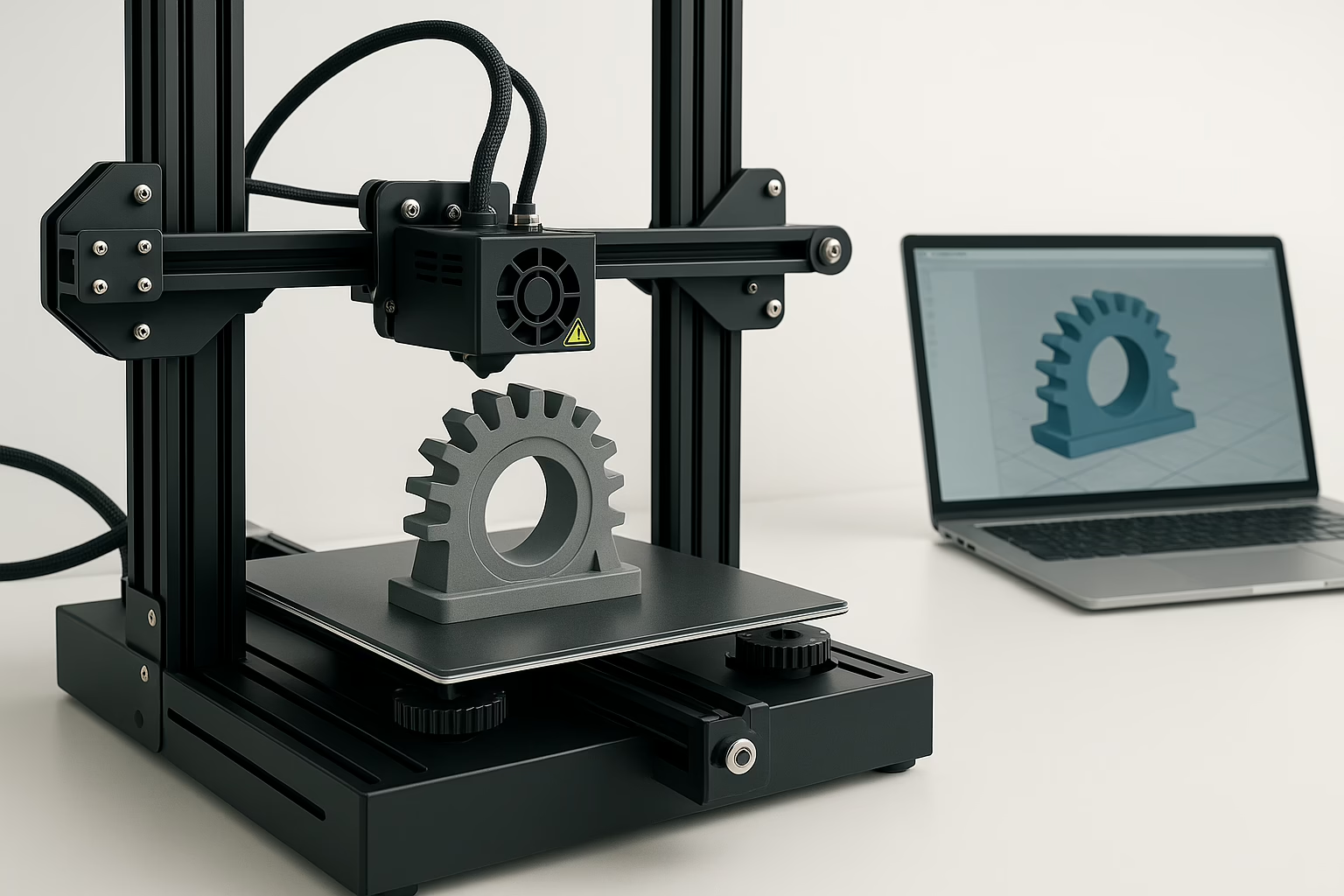
Explore the transformative power of 3D printing for DIY projects, from creating custom prototypes at home to mastering essential techniques and materials.

Discover how AI support agents are revolutionizing customer service by automating responses, enhancing efficiency, and improving satisfaction in the digital age.

Explore how AI is reshaping the workforce, impacting job markets, productivity, and energy consumption. Understand the challenges and opportunities ahead in a tech-driven future.

As AI transforms the workplace, understanding its impact on job roles and productivity is vital. Discover how this technology reshapes white-collar employment dynamics.

Explore the world of indoor gardening in 2025, where smart tech meets stylish design. Discover top systems that cater to every space and lifestyle.

Learn to set up Telegram notifications for Rundeck jobs using the rundeck-notify GoLang application. Get instant alerts for job events directly on your device.

Explore the power of Proxmox VE in building a scalable and flexible homelab, a vital tool for IT professionals refining their practical skills.

Learn to measure internet speed directly from your Sophos firewall, bypassing internal network issues. This guide covers essential CLI methods.

Revitalize your outdated security devices into useful tools for your smart home. Discover creative ways to repurpose old tech, saving money and reducing waste.

Practical guidance on choosing an MQTT broker for IoT, covering security, scalability, performance and migration.

Run Home Assistant without a Raspberry Pi: hardware options, HAOS or container installs, networking and maintenance.

When a mailbox is compromised, it can lead to a surge of spam and harmful emails, threatening your organization's reputation. This guide offers key steps to manage and clear the email spool on your Sophos XGS Firewall, including stopping the SMTP service and optimizing your database. Don’t let a compromised mailbox disrupt your operations—read on...

Setting up Apache2 with PHP on a Debian-based server is crucial for hosting websites or applications. Follow these steps for a smooth configuration.

Learn how to disable Remote Desktop Protocol (RDP) on Windows to minimize security risks. Follow these methods to ensure your system is protected.

Learn how to remove cached credentials on Windows 10 and 11 to enhance security and resolve login issues with this comprehensive guide for IT professionals.
Learn how to generate strong passwords using PowerShell with practical code samples and enhance your digital security

The GitHub repository CrowdStrike-BSOD-Fix offers a PowerShell script designed to fix the Blue Screen of Death (BSOD) caused by the CrowdStrike Falcon Sensor on Windows hosts.
Planes grounded, trains delayed, banks offline – it’s like the tech world decided to have a collective nap, leaving us all in the lurch.

In a world where cyber threats lurk in every corner of your inbox, email security is more crucial than ever. Learn how SPF, DKIM, and DMARC can protect your business. #EmailSecurity #CyberThreats #SPF #DKIM #DMARC

With the UK's 5G network expanding rapidly, businesses and consumers alike are set to experience a new era of connectivity. But what exactly does this mean for the average person and enterprises looking to leverage this technology?